User Activity Documentation Covering Anoceligt and Alerts Logs
User activity documentation, particularly through Anoceligt and alerts logs, serves as a foundational aspect of understanding digital interactions. Anoceligt logs reveal user patterns, enhancing service delivery. In contrast, alerts logs highlight potential security vulnerabilities. Analyzing these logs can lead to strategic insights for organizations. However, the effectiveness of this documentation hinges on the methodologies employed in tracking user activity. What best practices can ensure comprehensive monitoring and improved outcomes?
Understanding Anoceligt Logs
While many users may interact with systems on a daily basis, the analysis of Anoceligt logs provides critical insights into user behavior and system performance.
Understanding Anoceligt definitions and conducting thorough log interpretation enables organizations to identify patterns, optimize interactions, and enhance system efficiency.
This systematic approach empowers users, fostering an environment where informed decisions can be made based on accurate data analysis.
The Role of Alerts Logs in Security
Alerts logs play a pivotal role in security management by providing a comprehensive record of system events that may indicate potential threats or breaches.
The alert significance lies in their ability to highlight anomalies, enabling proactive measures. Understanding security implications derived from these logs is essential for mitigating risks and enhancing overall system integrity.
Consequently, alerts logs serve as vital tools for informed decision-making in security protocols.
Analyzing User Behavior Through Documentation
How can organizations effectively understand user behavior through meticulous documentation?
By analyzing user engagement data and identifying behavior patterns, organizations can gain valuable insights into user preferences and habits.
This systematic approach enables them to enhance services, improve user experience, and foster a sense of autonomy.
Ultimately, thorough documentation serves as a crucial tool for organizations seeking to adapt to the evolving needs of users.
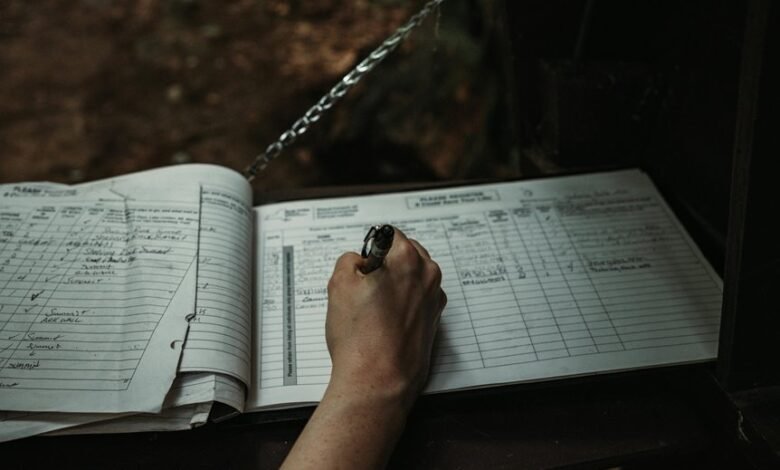
Best Practices for Effective User Activity Tracking
Effective user activity tracking requires a systematic approach that prioritizes accuracy and relevance. Implementing diverse tracking methods while safeguarding user privacy is essential.
Organizations should ensure transparent communication regarding data collection practices and provide users the option to manage their preferences.
Regularly reviewing tracking mechanisms enhances effectiveness and fosters trust, ultimately aligning user freedom with the organization’s objectives in monitoring activity.
Conclusion
In conclusion, the convergence of Anoceligt and alerts logs underscores their significance in understanding user behavior and enhancing system security. As organizations increasingly rely on these logs, a coincidental synergy emerges; insights gleaned from user interactions not only inform service improvements but also bolster security protocols. This dual purpose illustrates how comprehensive user activity documentation can transform potential vulnerabilities into opportunities for growth, ultimately fostering a resilient digital environment that aligns organizational objectives with user expectations.






